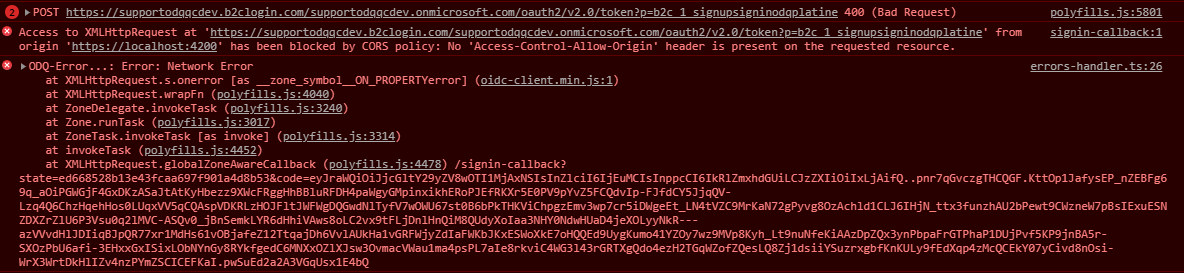
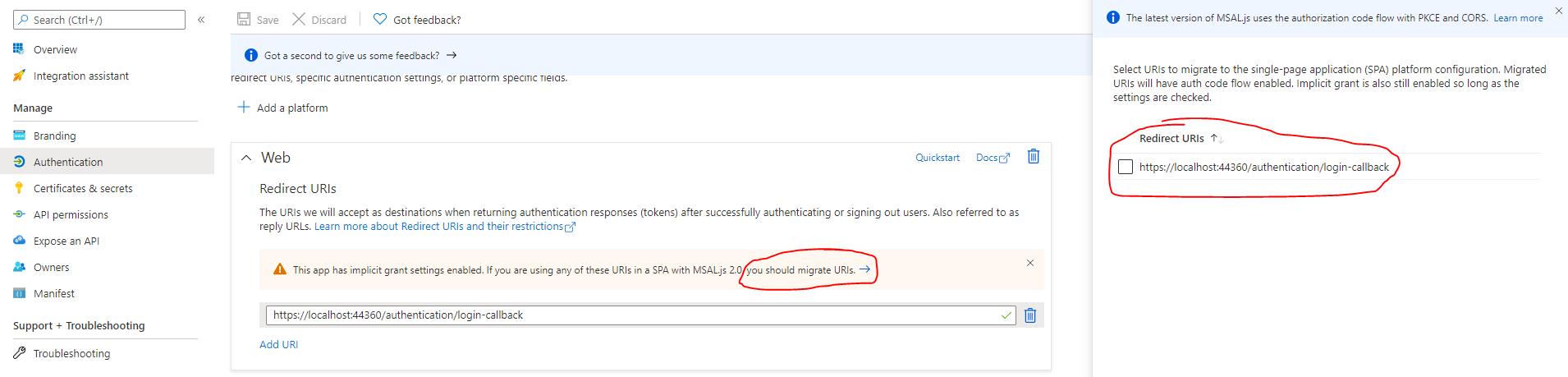
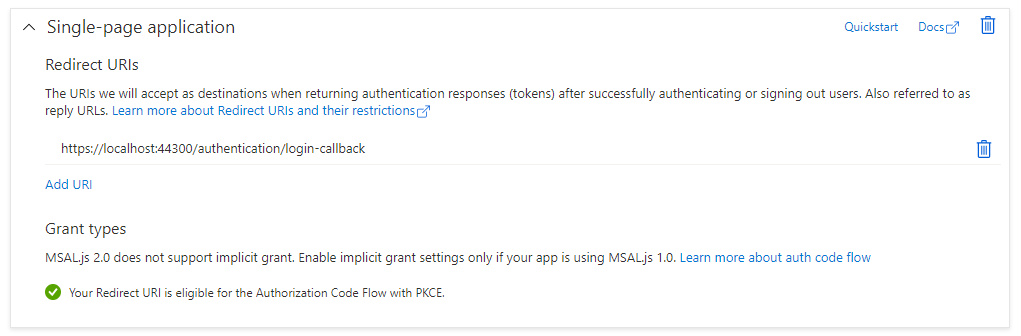
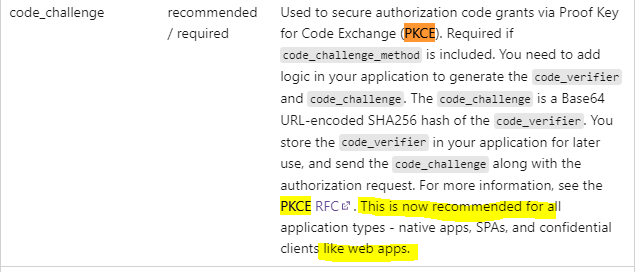
I try to setup authentification for an Angular app using authorization code and Azure AD B2C (oidc-client on client side), but I'm getting these errors from Angular:
After looking in B2C audit logs, I found this error message:
Clients must send a client_secret when redeeming a confidential grant.
Here's my client side configuration:
const settings = {
stsAuthority: 'https://supportodqqcdev.b2clogin.com/supportodqqcDev.onmicrosoft.com/v2.0/.well-known/openid-configuration?p=B2C_1_SignUpSignInOdqPlatine',
clientId: '8447df5b-35a0-40a7-944f-5dcce87a2193',
clientRoot: 'https://localhost:4200',
scope: 'openid https://supportodqqcDev.onmicrosoft.com/platineclientdev/read',
};
this.userManager = new UserManager({
authority: settings.stsAuthority,
client_id: settings.clientId,
redirect_uri: `${settings.clientRoot}/signin-callback`,
scope: settings.scope,
response_type: 'code',
post_logout_redirect_uri: `${settings.clientRoot}/signout-callback`,
automaticSilentRenew: true,
silent_redirect_uri: `${settings.clientRoot}/assets/signin-silent-callback.html`,
});
If I switch the above configuration to use a local IdentityServer instance, everthings works has expected.
Is someone able to point me out where or how I should investigate this?