I have aplication in java and cxf which connects to WebServices with client certificate.
I got certificates form WebService owner
- certificate.p12
- certificate.pem
- certificate.crt
- trusted_ca.cer
- root_ca.cer
I have problem with straightforward converting this p12 certficate to working jks keystore requred by java.
I did this:
keytool -importkeystore -srckeystore certificate.p12 -srcstoretype PKCS12 -destkeystore certificate1.jks -deststoretype JKS -storepass secret
keytool -import -alias root -file root_ca.cer -trustcacerts -keystore certificate1.jks -storepass secret
keytool -import -alias trusted -file trusted_ca.cer -trustcacerts -keystore certificate1.jks -storepass secret
but this jks doesn`t work and I get HTTP response '403: Forbidden' when using this certificate1.jks
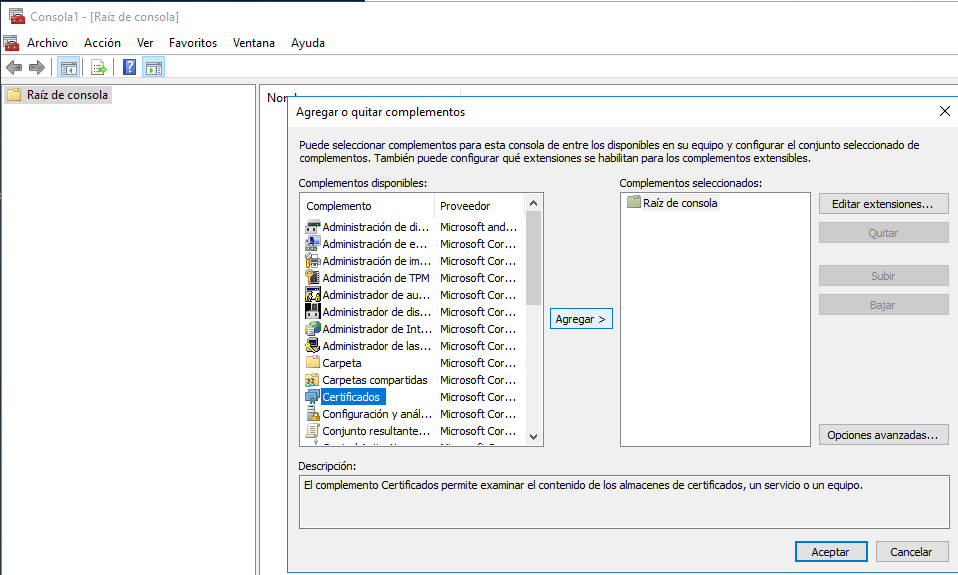
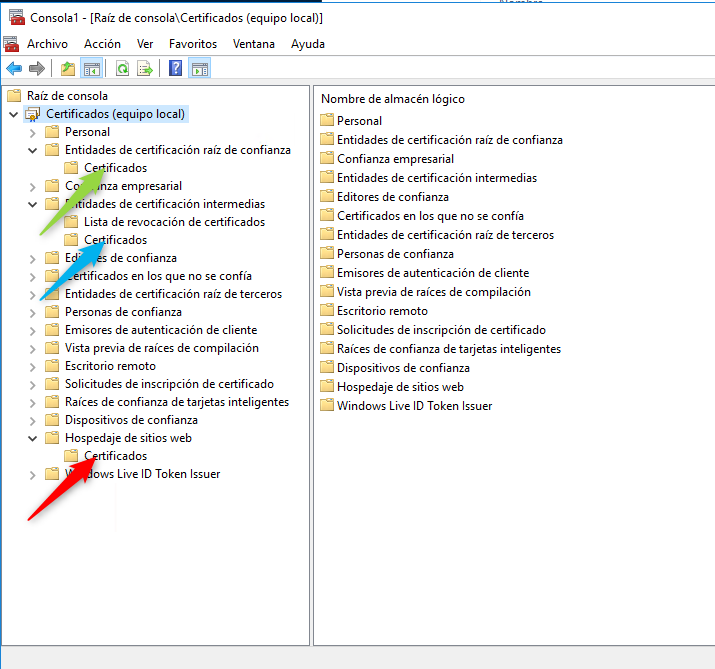
However if I import this p12(pfx) certificate to Internet Explorer and then export this certificate from IE to pfx format selecting "Include all certificates in the certification path" checkbox and use:
keytool -importkeystore -srckeystore certificate.pfx -srcstoretype PKCS12 -destkeystore certificate2.jks -deststoretype JKS -storepass secret
keytool -import -alias root -file root_ca_kir.cer -trustcacerts -keystore certificate2.jks -storepass secret
keytool -import -alias trusted -file trusted_ca_kir.cer -trustcacerts -keystore certificate2.jks -storepass secret
Then everything works fine and I can connect to WebService using certificate2.jks.
I found that original certificate.p12(pfx) contains only one entry (Certificate chain length: 1):
keytool -list -keystore certificate.p12 -storepass secret -storetype PKCS12 -v
*******************************************
*******************************************
Alias name: alias
Entry type: PrivateKeyEntry
Certificate chain length: 1
Certificate[1]:
Owner: CN=MyCompany, [email protected], O=bla, C=PL
Issuer: CN=Trusted CA, O=ble, C=PL
Serial number: xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
Valid from: ... until: ...
Certificate fingerprints:
MD5: XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX
SHA1: XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX
Signature algorithm name: SHA1withRSA
Version: 3
Extensions:
#1: ObjectId: X.X.XX.XX Criticality=false
KeyUsage [
DigitalSignature
Key_Encipherment
]
...
*******************************************
*******************************************
while certificate.pfx exported from IE with "Include all certificates in the certification path" contains certificate chain with second Trusted CA certificate (Certificate chain length: 2):
keytool -list -keystore certificate.p12 -storepass secret -storetype PKCS12 -v
*******************************************
*******************************************
Alias name: alias
Entry type: PrivateKeyEntry
Certificate chain length: 2
Certificate[1]:
Owner: CN=MyCompany, [email protected], O=bla, C=PL
Issuer: CN=Trusted CA, O=ble, C=PL
Serial number: xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
Valid from: ... until: ...
Certificate fingerprints:
MD5: XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX
SHA1: XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX
Signature algorithm name: SHA1withRSA
Version: 3
Extensions:
#1: ObjectId: X.X.XX.XX Criticality=false
KeyUsage [
DigitalSignature
Key_Encipherment
]
...
Certificate[2]:
Owner: CN=Trusted CA, O=ble ble ble, C=PL
Issuer: CN=ROOT CA, O=ble ble ble, C=PL
Serial number: xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx
Valid from: ... until: ...
Certificate fingerprints:
MD5: XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX
SHA1: XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX:XX
Signature algorithm name: SHA1withRSA
Version: 3
Extensions:
*******************************************
*******************************************
So to solve my problem I need to have p12 certificate with chain to trusted CA certificate. I can do this by importing p12 to IE and then exporting back with "Include all certificates in the certification path".
How can I do this without IE using keytool or other tool?
Bary

-nokeysoption to the last command. I have OpenSSL 1.0.1e-fips 11 Feb 2013 – Sharpe