I'm answering this question in regards to a Java project that requires notarization. With slight modifications, the answer should work for other types of projects (python, powershell, node) as well.
Note: At the time of posting this, Apple's notarization command allowed the below procedure to work however as notarization and security becomes more common and more strictly enforced it is inevitable that Apple will change and improve hardening requirements and procedures. Please edit, comment or re-answer as needed.
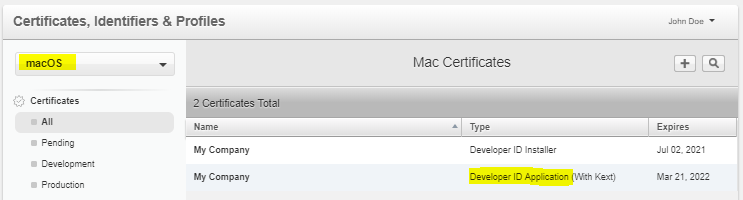
Code Signing
Notarization
Once the native libraries are signed the package must be sent for notarization using xcrun.
xcrun altool --eval-app --primary-bundle-id <bundle id> -u <iTunes Connect Account> -f <file path>
Which may look something like this:
xcrun altool --eval-app --primary-bundle-id com.domain.appname -u [email protected] -f appname.pkg
You will be prompted for your Apple Developer password (NOT the password you use to login to your Mac). Edit: Since dual-factor has been mandated, you'll need to create an app-specific password for this step!
After a few minutes, the xcrun command will return a unique ID that can be used to determine if the notarization was approved.
RequestUUID = a1b2c3d4e5-a1b2-a1b2-a1b2-a1b2c3d4e5f6
- Periodically check the status of this unique ID to see if it was approved or denied.
xcrun altool --eval-info a1b2c3d4e5-a1b2-a1b2-a1b2-a1b2c3d4e5f6 -u [email protected]
If denied, they won't directly tell you why, you have to parse the JSON response.
LogFileURL: https://osxapps-ssl.itunes.apple.com/itunes-assets/...
Read the JSON and correct the problems identified. The JSON is minified, you may want to run it through a pretty-formatter. If there are no problems, your app has been notarized and is Ready for distribution.
{
"logFormatVersion": 1,
"jobId": "a1b2c3d4e5-a1b2-a1b2-a1b2-a1b2c3d4e5f6",
"status": "Accepted",
"statusSummary": "Ready for distribution",
"statusCode": 0,
"archiveFilename": "appname.pkg",
"uploadDate": "2018-10-26T05:41:12Z",
"sha256": "e2350bda66...",
"issues" null
}
Stapling
Finally, stapling the build will ensure the package is trusted even when a network connection is not available.
(apple.com) You should also attach the ticket to your software using the stapler tool, so that future distributions include the ticket. This ensures that Gatekeeper can find the ticket even when a network connection isn’t available. To attach a ticket to your app, use the stapler tool:
xcrun stapler staple appname.pkg
Runtime
An additional solution provided by @NaderNader, if bundling the Java runtime along with a .app, additional steps are needed to mark the distribution as a runtime using the --option=runtime flag, where P6DMU6694X is your signing ID:
codesign --force --deep --options=runtime -s "P6DMU6694X" /path/to/My.app

--options runtimehandles this. This is a good start. My.pkghas shell scripts for install and launch but just one big fat jar file. Some components are.dylib/.sowith JNI (Java Native Interface) bundled. Java (already installed on the system) will run these. I have no idea how to fulfil these new requirements. :/ – Periodontal.pkgfor evaluation -- making no changes -- usingxcrun altool --eval-app --primary-bundle-id <com.mysite.myapp> -u <myappleid@mydomain> -f <path/to/myapp.pkg>and after a minute or so, it returnedRequestUUID = a1b2c3d4e5-a1b2-a1b2-a1b2-a1b2c3d4e5f6which apparently I have to monitor usingxcrun altool --eval-info a1b2c3d4e5-a1b2-a1b2-a1b2-a1b2c3d4e5f6 -u <[email protected]>or via email. Note, the User Agreement had changed on developer.apple.com, so I signed in and agreed before attempting. – Periodontal--eval-infocommand mentioned above) explains why. Compiled objects (.dylib,.jnilib, NOT scripts, NOT JAR files) that come with some 3rd-party Java libraries we bundle aren't signed. We'll modify our build system to sign these and see how much further we get. My (speculative) anticipation is that Apple (currently) only cares about hardening compiled objects, so we'll start there. – Periodontal