I need to remove excessive headers (primarily to pass penetration testing). I have spent time looking at solutions that involve running UrlScan, but these are cumbersome as UrlScan needs to be installed each time an Azure instance is started.
There must be a good solution for Azure that does not involve deploying installers from startup.cmd.
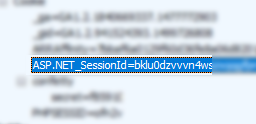
I understand that the response headers are added in different places:
- Server: added by IIS.
- X-AspNet-Version: added by System.Web.dll at the time of Flush in HttpResponse class
- X-AspNetMvc-Version: Added by MvcHandler in System.Web.dll.
- X-Powered-By: added by IIS
Is there any way to configure (via web.config etc.?) IIS7 to remove/hide/disable the HTTP response headers to avoid the "Excessive Headers" warning at asafaweb.com, without creating an IIS module or deploying installers which need to be run each time an Azure instance starts?