I'm stuck behind a firewall, so I have to use HTTPS to access my GitHub repository. I'm using Cygwin 1.7.7 on Windows XP.
I've tried setting the remote to https://[email protected]/username/ExcelANT.git, but pushing prompts for a password, but it doesn't do anything once I've entered it.
https://username:<password>github.com/username/ExcelANT.git and cloning the empty repository from scratch, but each time it gives me the same error:
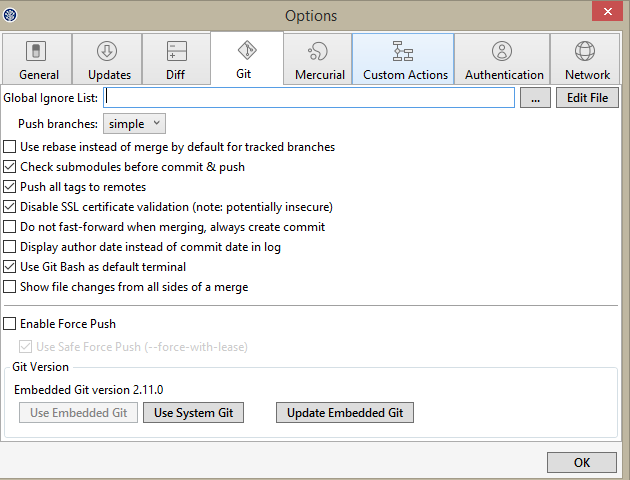
error: SSL certificate problem, verify that the CA cert is OK. Details: error:14090086:SSL routines:SSL3_GET_SERVER_CERTIFICATE:certificate verify failed while accessing https://github.com/username/ExcelANT.git/info/refs
Turning on GIT_CURL_VERBOSE=1 gives me
* About to connect() to github.com port 443 (#0) * Trying 207.97.227.239... * successfully set certificate verify locations: * CAfile: none CApath: /usr/ssl/certs * SSL certificate problem, verify that the CA cert is OK. Details: error:14090086:SSL routines:SSL3_GET_SERVER_CERTIFICATE:certificate verify failed * Expire cleared * Closing connection #0 * About to connect() to github.com port 443 (#0) * Trying 207.97.227.239... * successfully set certificate verify locations: * CAfile: none CApath: /usr/ssl/certs * SSL certificate problem, verify that the CA cert is OK. Details: error:14090086:SSL routines:SSL3_GET_SERVER_CERTIFICATE:certificate verify failed * Expire cleared * Closing connection #0 error: SSL certificate problem, verify that the CA cert is OK. Details: error:14090086:SSL routines:SSL3_GET_SERVER_CERTIFICATE:certificate verify failed while accessing https://github.com/username/ExcelANT.git/info/refs
fatal: HTTP request failed
Is this a problem with my firewall, Cygwin or what?
I hadn't set the HTTP proxy in the Git configuration. However, it's an ISA server that needs NTLM authentication, not basic, so unless anyone knows how to force Git to use NTLM, I'm scuppered.