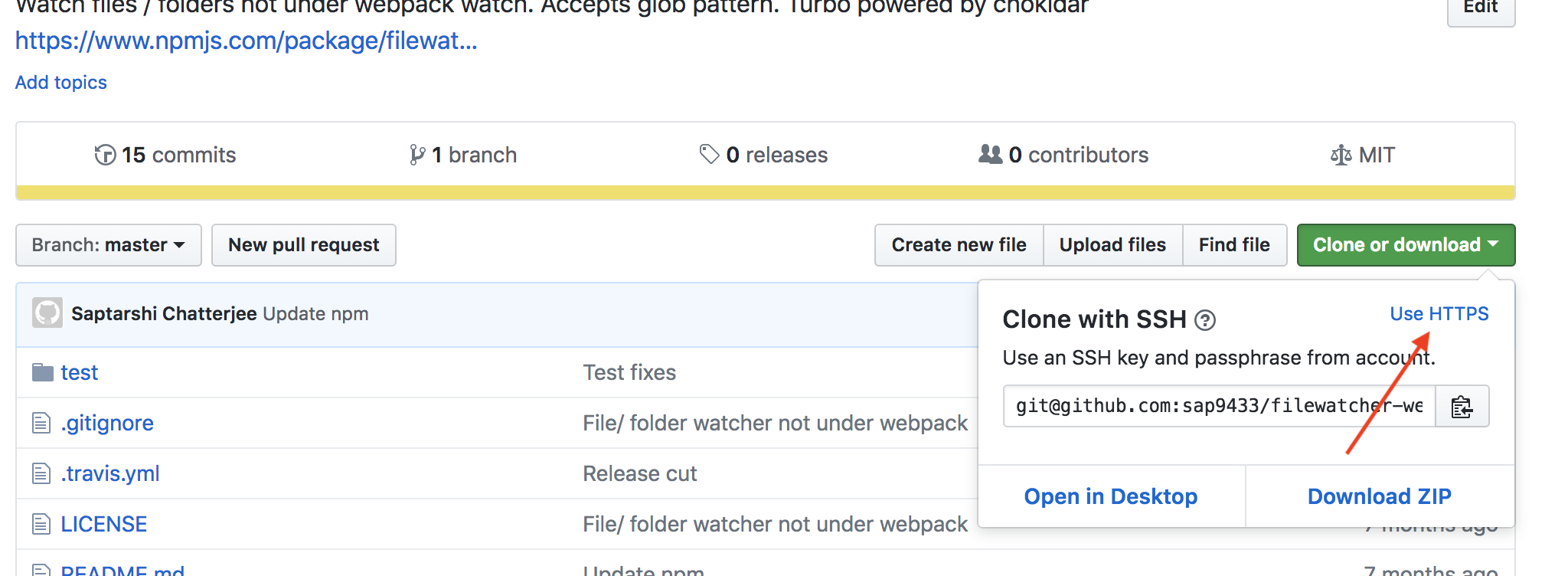
If you're using SSH and your private key is encrypted with a passphrase, then you'll still be prompted to enter the passphrase/password for the private key when you do network operations with Git like push, pull, and fetch.
Use ssh-agent to save the private key passphrase/password credentials
If you want to avoid having to enter your passphrase every time, you can use ssh-agent to store your private key passphrase credentials once per terminal session, as I explain in my answer to Could not open a connection to your authentication agent:
$ eval `ssh-agent -s`
$ ssh-add
In a Windows msysgit Bash, you need to evaluate the output of ssh-agent, but I'm not sure if you need to do the same in other development environments and operating systems.
ssh-add looks for a private key in your home .ssh folder called id_rsa, which is the default name, but you can pass a filepath to a key with a different name.
Killing the agent
When you're done with your terminal session, you can shutdown ssh-agent with the kill flag -k:
$ ssh-agent -k
As explained in the ssh-agent manual:
-k
Kill the current agent (given by the SSH_AGENT_PID environment variable).
Optional timeout
Also, it can take an optional timeout parameter like so:
$ ssh-add -t <timeout>
where <timeout> is of the format <n>h for <n> hours, <n>m for <n> minutes, and so on.
According to the ssh-agent manual:
-t life
Set a default value for the maximum lifetime of identities added to the agent. The lifetime may be specified in seconds or in a
time format specified in sshd_config(5). A lifetime specified for an identity with ssh-add(1) overrides this value. Without this option the default maximum lifetime is forever.
See this page for more time formats.
Security warning for Cygwin users
Cygwin users should be aware of a potential security risk with using ssh-agent in Cygwin:
people should be cognizant of the
potential dangers of ssh-agent under Cygwin 1, though under a local netstat and remote portscan it does not appear that the port specified in /tmp/ssh-foo is accessible to anyone ...?
[1]: http://www.cygwin.com/ml/cygwin/2001-01/msg00063.html
And at the cited link:
however, note that Cygwin's Unix domain sockets are FUNDAMENTALLY INSECURE and so I strongly DISCOURAGE usage of ssh-agent under Cygwin.
when you run ssh-agent under Cygwin it creates AF_UNIX socket in /tmp/ssh-$USERNAME/ directory. Under Cygwin AF_UNIX sockets are emulated via AF_INET sockets. You can easily see that if you'll look into /tmp/ssh-$USERNAME/agent-socket-* file via Notepad. You'll see something like
!<socket >2080
then run netstat -a and surprise! You have some program listening to port 2080. It's ssh-agent. When ssh receives an RSA challenge from the server, it refers to corresponding /tmp/ssh-$USERNAME/agent-socket-* (under Cygwin, in our case, that means it'll open connection to localhost:2080) and asks ssh-agent to process the RSA challenge with the private key it has, and then it simply passes the response received from the ssh-agent to the server.
Under Unix, such a scenario works without problems, because the Unix kernel checks permissions when the program tries to access an AF_UNIX socket. For AF_INET sockets, however, connections are anonymous (read
"insecure"). Imagine, that you have the Cygwin ssh-agent running. A malicious hacker may portscan your box, locate open port used by ssh-agent, open a connection to your SSH server, receive the RSA challenge from it, send it to your ssh-agent via an open port he/she found, receive the RSA response, send it to the SSH server and voila, he/she successfully logged in to your server as you.